Identity Platform with Microsoft Active Directory® Advanced based on Windows Server® 2016 is a directory service developed by Microsoft for Windows domain networks. It is included in most Windows Server operating systems as a set of processes and services.
This is a quick deployment and ready-to-run image.
Simple and rapid installation. Easy to maintain.
The guide how to work with the Identity Platform with Microsoft Active Directory® Advanced based on Windows Server® 2016
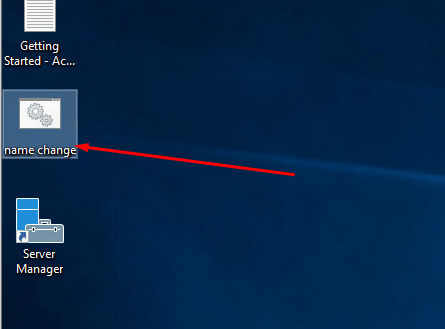
After purchasing and turning on the VM, you need to run the “name change” file on the desktop, and restart the VM.
- Right-click the network icon in the bottom right of the Task Bar and select Open Network and Sharing Center from the menu.
- In the Network and Sharing Center, click <Change adapter settings>.
- On the Network Connections screen, right-click the network adapter for which you want to change the IP address and select Properties
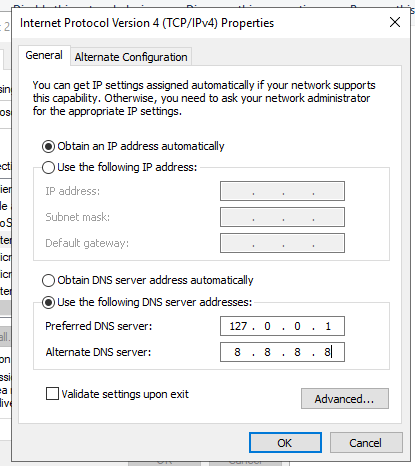
- Select Internet Protocol Version 4 (TCP/IPV4) and click <Properties>
- Fill in your private IPV4 ip address, subnet mask, default gateway or just leave the default values.
- Fill in the preferred DNS server as (127.0.0.1) which is known as your local host IP.
- The alternate DNS server address will be the IP address of another domain controller you have in your forest. If you don’t have any setup yet, you can leave this blank and update later if you are going to set up other domain controllers.
After you click <OK> you will be automatically disconnected from the VM. You will need to restart the VM, wait a little and reconnect using the same details.
Active Directory Installation Steps
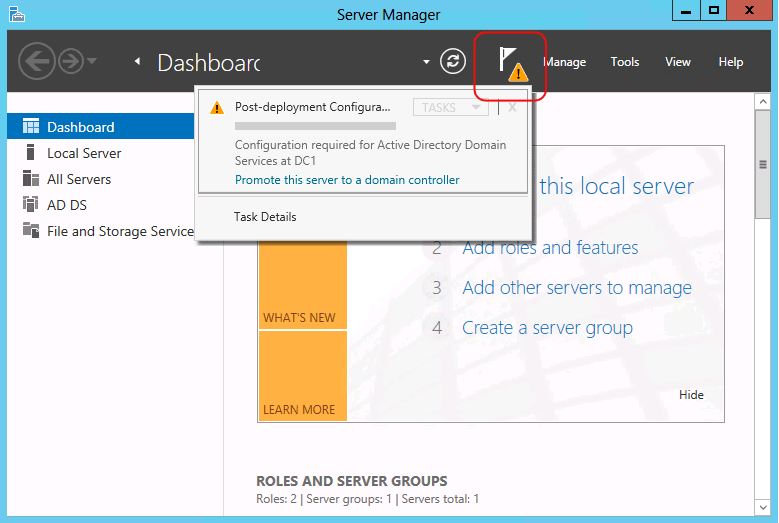
Open up Server Manager and click on the yellow notification and select promote this server to a domain controller.
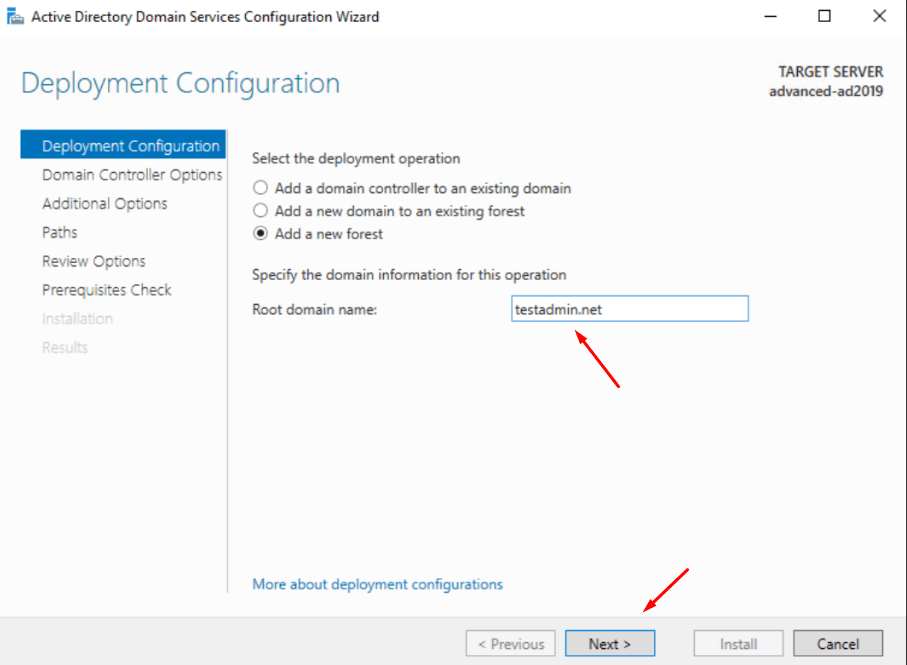
This will start the active directory configuration wizard. The next demo shows how to set up a new forest. But if you add this to an existing domain you can choose the relevant option. Select the option to add a new forest and type FQDN for the domain. Then click <next>.
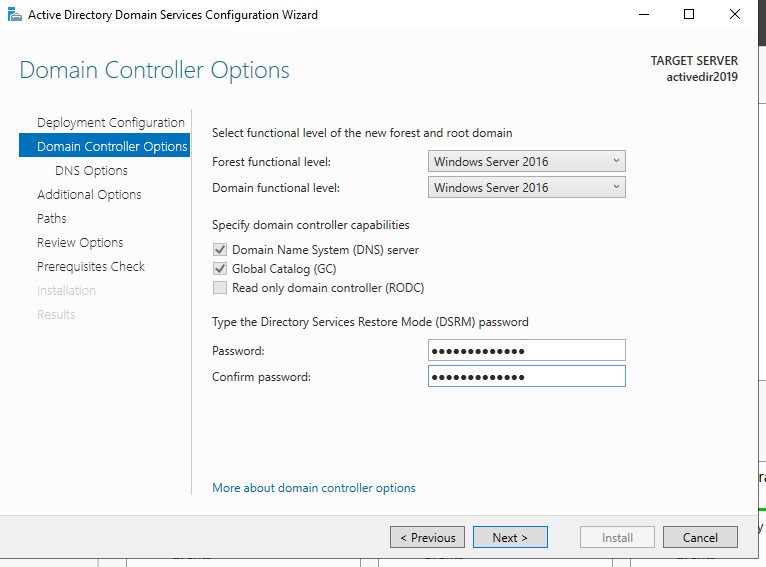
At this and the next stages, the system may not respond for some time. In this case, you should wait until everything is loaded. On the next page you can select the domain and forest functional levels. Then type a password for DSRM. Then click <next>.
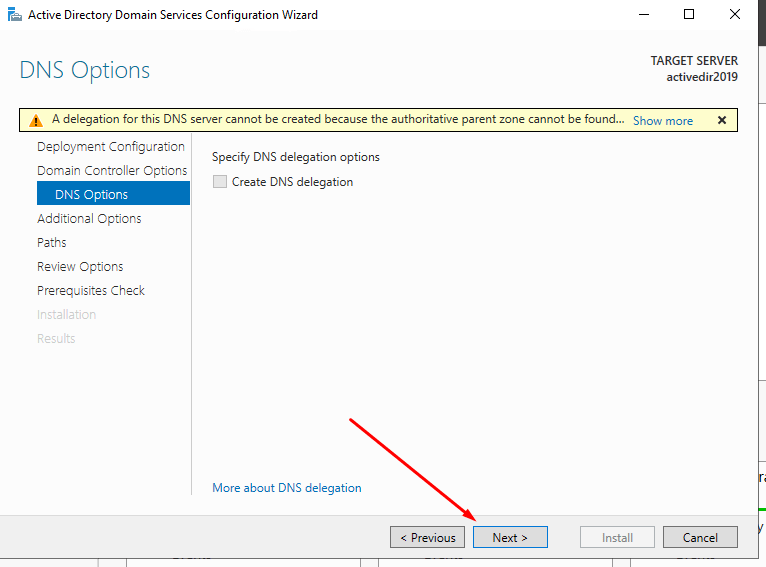
Since we are creating the first DNS server in the new forest, it is not necessary to select additional parameters and click <next> to proceed.
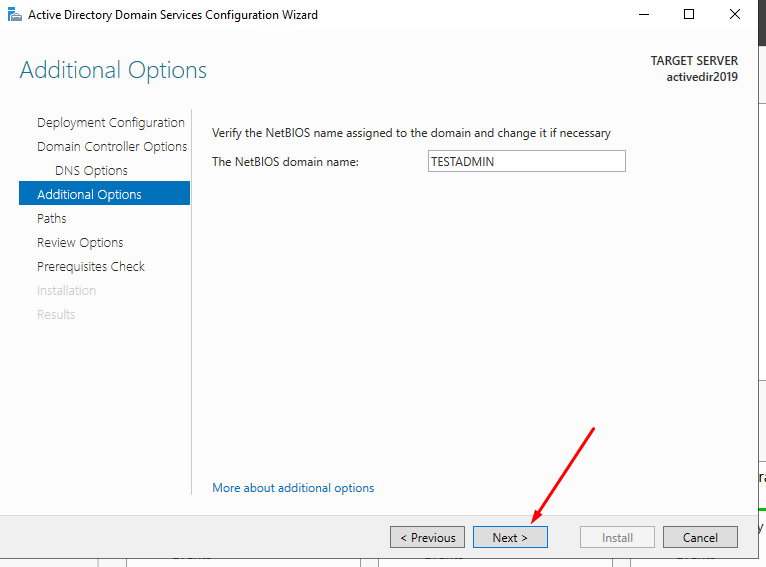
For the NETBIOS name keep the default and click <next>.
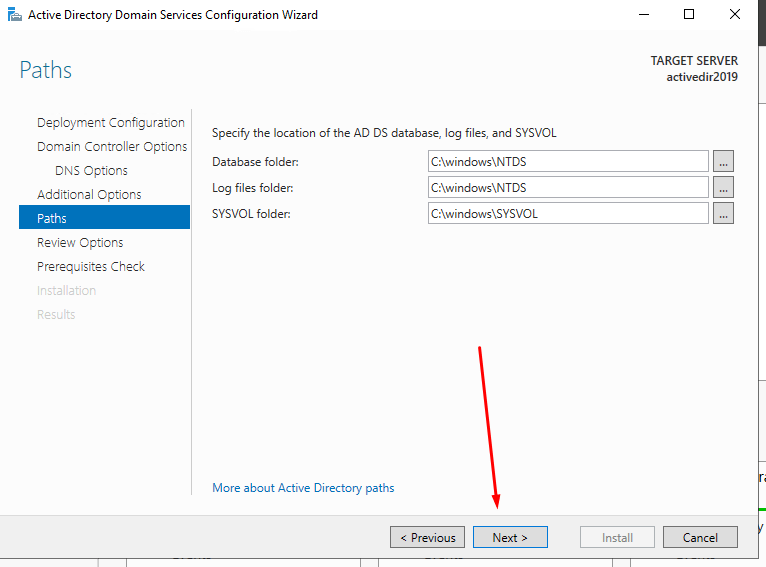
Next page is to define the NTDS, SYSVOL and LOG file folders. You can keep default or define different paths for these. This demo shows how to keep the default paths. Once changes are done, click <next> to continue.
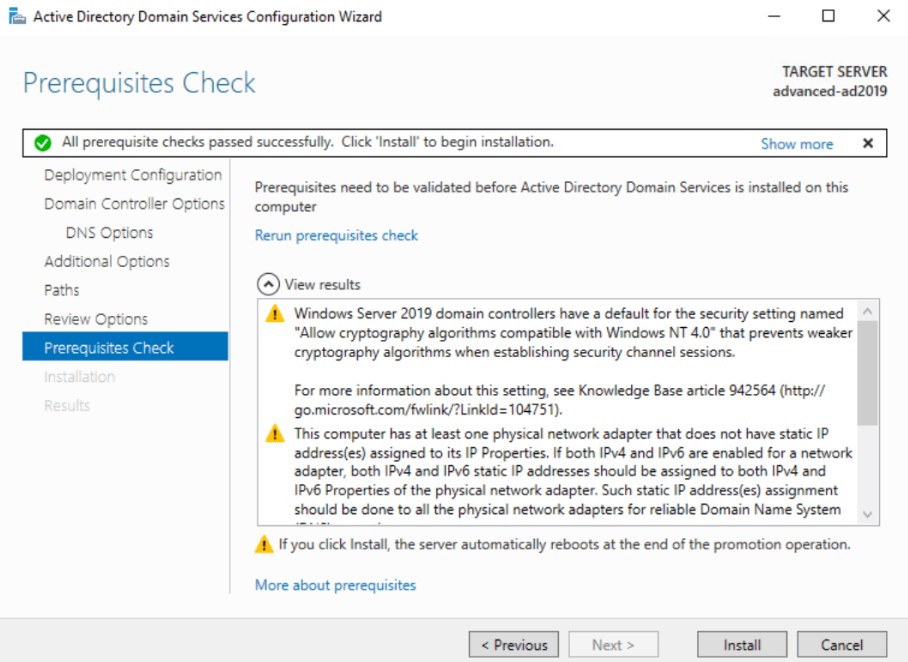
On the next window the prerequisite check will be done.
If it passes, it will enable the option to install. Click on the <install> button to begin the installation process.
Then the installation process of promoting this server to a Windows domain controller will be started.
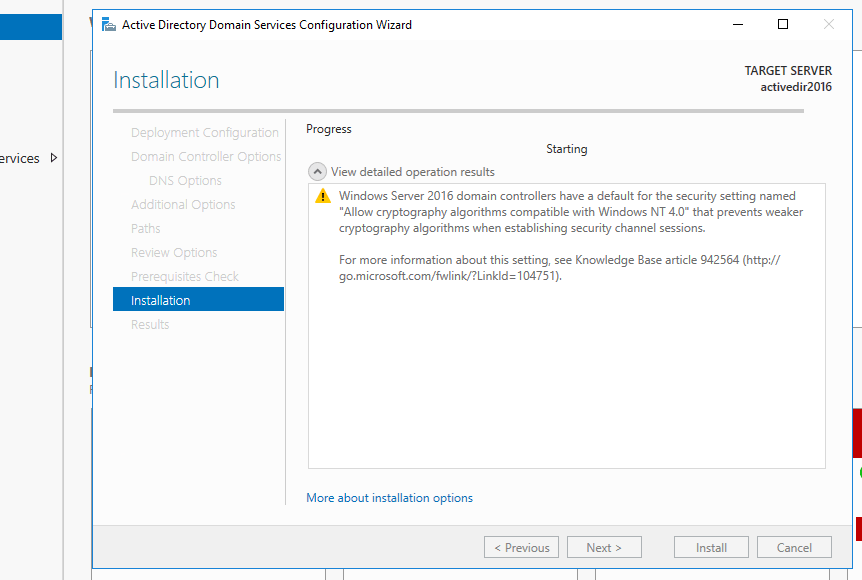
After the AD installation, The server will restart automatically. Once it comes back online, log in to the server as domain administrator.
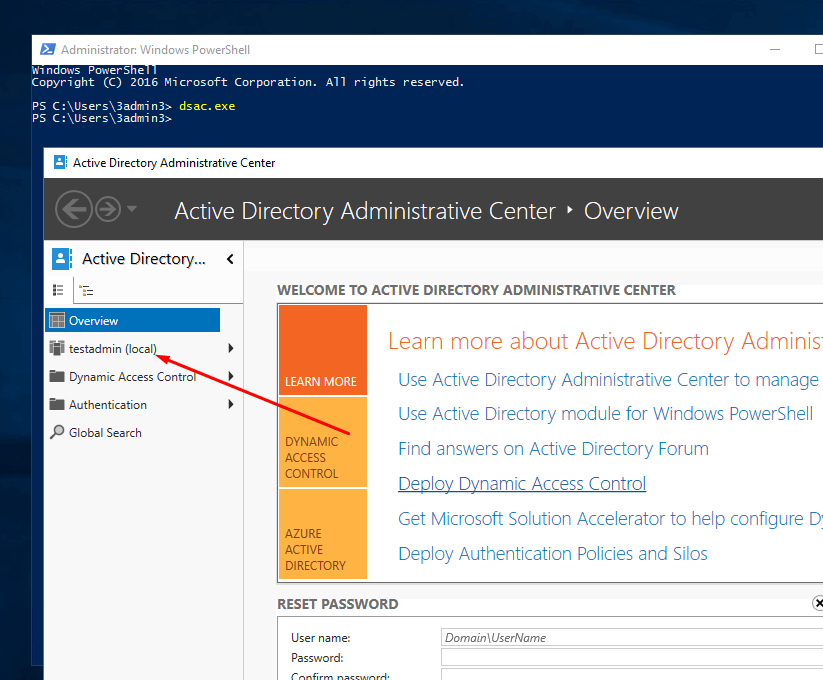
Once logged in, open powershell (as administrator) and type dsac.exe and press enter. It will open up the active directory administrative center. Here you can start managing the domain resources.
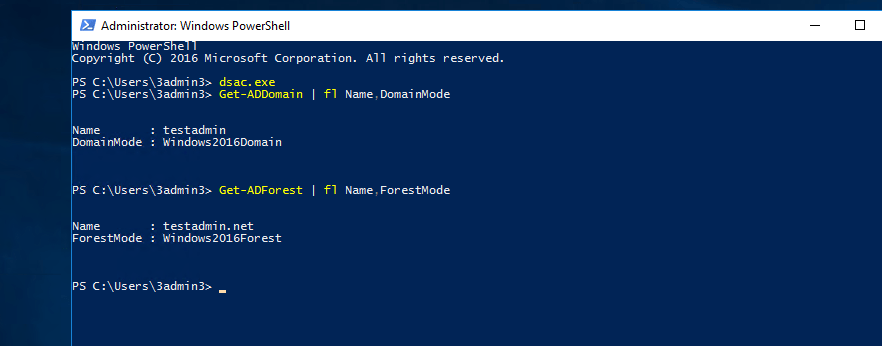
Also you can use Get-ADDomain | fl Name,DomainMode and Get-ADForest | fl Name,ForestMode from powershell to confirm the domain and forest functional levels.
Active Directory Firewall Ports
In order to your domain controllers to communicate with other domain controllers in your Active Directory, you will need to make sure the following firewall ports are open between domain controllers in your cloud environment or on premises domain if you have a hybrid setup:
- RPC endpoint mapper: port 135 TCP, UDP
- NetBIOS name service: port 137 TCP, UDP
- NetBIOS datagram service: port 138 UDP
- NetBIOS session service: port 139 TCP
- SMB over IP (Microsoft-DS): port 445 TCP, UDP
- LDAP: port 389 TCP, UDP
- LDAP over SSL: port 636 TCP
- Global catalog LDAP: port 3268 TCP
- Global catalog LDAP over SSL: port 3269 TCP
- Kerberos: port 88 TCP, UDP
- DNS: port 53 TCP, UDP
To setup Azure firewall rules refer to – Azure Network Security Groups
