Filezilla FTP Secured Server for Windows 2016 is a powerful tool for data transfer. it’s easy to transfer even the huge data. Transfer the sensitive data using the SSL/TLS encryption quickly and securely.
This is a quick deployment and ready-to-run image.
Simple and rapid installation. Easy to maintain.
The guide how to work with the Filezilla FTP Secured Server for Windows 2016
Start up Filezilla Server Instance
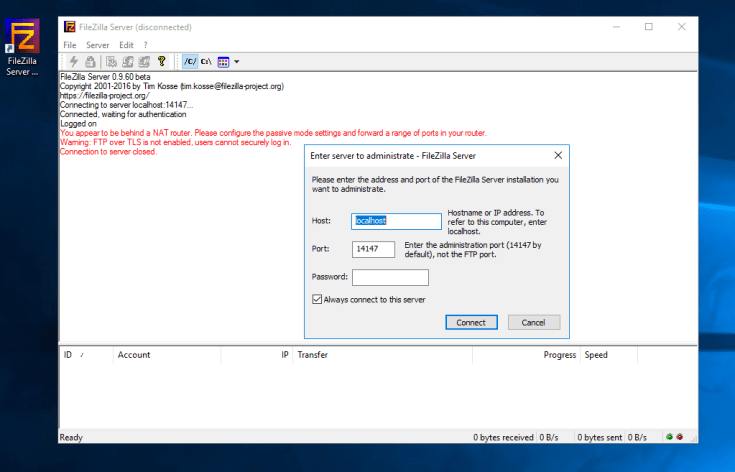
Start up the Filezilla Server Instance application, with the shortcut on your desktop. In the pop up window click Connect as displayed below (the password field is empty):
Passive Mode Settings
When the connection has been established, it’s possible that some errors may occur, that is okay ‘cause some more steps should be done. From the options select
> Edit > Settings > Passive Mode Settings
Then it’s necessary to set a passive mode port range. Typically (50000-51000) ports are used when transferring data to the server.
Set Public IP Address
To allow the third-party clients to connect – ensure that your VM has the correct public IP Address (in our case it is 40.114.31.95).
If you faced the problem with attaching the public IP Address, follow the Microsoft’s Guide.
Whenever you have associated the public IP address with the NIC on your Azure VM, attach the IP Address to the Passive Mode Settings, as displayed below (highlighted in green), and also the Passive Port Range:

Set up Local Users
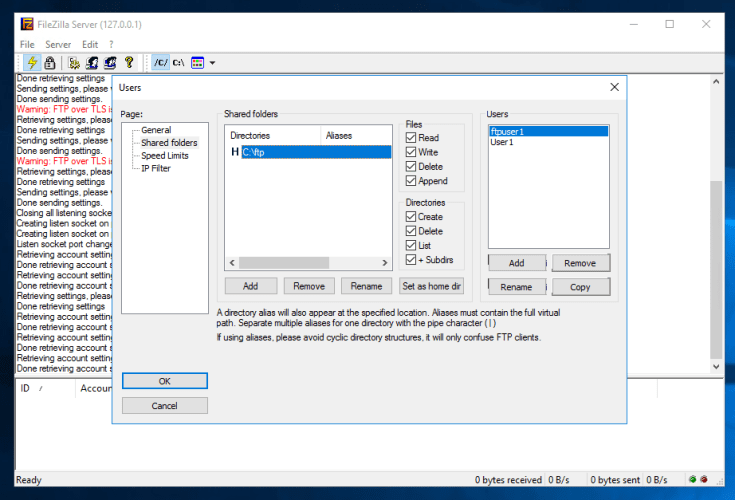
To set up local users and give them access to the directories locally on your server you need to select Edit > Users
This is how new users can be joined and their passwords created.
After that, provide the users with the access to the necessary local folders.
There is the pre-configured folder on the VM, located on the C:\FTP Directory which can be used. Also you can setup any amount of folders that you need as well. Moreover, you can setup the groups with the permissions according to their status.
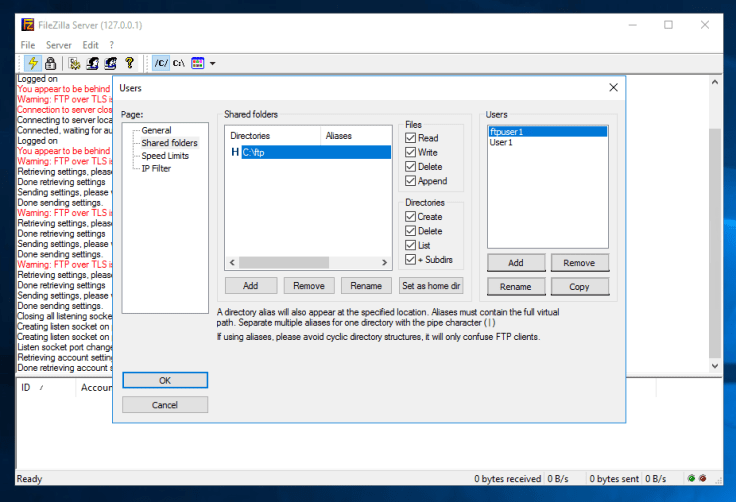
The next step is to assign these users to the needed FTP directories. Go to Shared Folder in the Users Menu and attach the local folders and designate the needed permissions:
Now it’s high time to test if you can connect using the FTP Client. If it’s impossible to connect, try the next options to adjust any NSG / Firewall rules.
NSG Rules / Firewall Rules Adjustments
In case you have NSG’s or Firewall appliances in Azure you’ll have to open access to the next ports:
- Port: 21 (Used for FTP)
- Port: 990 (Used for FTPS)
- Port: 14147 (Used for FTP Server Administration)
- Passive Port Range: 50000 – 51000 (Used when transferring data)
Client FTP Software
Users can use any FTP Client to allow clients to connect. One of the best solutions is to choose FileZilla’s FTP Client.
To connect to FileZilla’s FTP Client you should enter the IP of your VM in the <Host> field and the username and the password to the corresponding fields as well.


After starting the connection, a window with a certificate will appear, in it you must select the <Always trust certificate> item and click <OK>

After that, you will be connected to the FTP server.
Support
If you faced any problems at setting up the server this way, feel free to leave your comment below.
Contact us in case you would like to use our Managed Azure Service and allow us to manage your VM’s.
If you want us to help you to implement this FTP Server Solution into your environment and make all the configurations, please contact us. We will help you with this as soon as possible.
Disclaimer
This FTP Server solution was built with a help of the altered version of the FileZilla Server Opensource Software. This solution is allowed under the GPLv2 Licence. The original trademarks are owned by the relevant companies. Therefore, no warranty is included with this software.
Use it at your own risk, and if there any damages appear resulting from the use of this software, they will be entirely on your responsibility.